A Rose by Any Other Name...
October 22, 2015
One
riddle often heard in my
childhood was, "Who's buried in
Grant's tomb?" Although the remains of
Ulysses S. Grant (1822-1885), the 18th
President of the United States, and his
wife,
Julia Grant (1826-1902) are in this
Manhattan monument, they're not
buried there; rather, they are
entombed.
What sounds like a nearly equivalent riddle, "Who wrote the works of
William Shakespeare," is a
question that's been argued for nearly two hundred years. Some claim that Shakespeare was the
literary equivalent of the
mathematician,
Nicolas Bourbaki. Just as Bourbaki was the
pseudonym of a group of
20th century mathematicians, some have claimed that Shakespeare was the pseudonym for one or more
authors who chose to remain
anonymous.

The Cobbe portrait of William Shakespeare (1564-1616), thought to have been painted circa 1610, during his lifetime.
The Cobbe portrait is similar in likeness to the Droeshout engraving of Shakespeare that appears in the First Folio of 1623, albeit with a little more hair.
(Via Wikimedia Commons.)
The
circumstantial evidence for the claim that Shakespeare did not write Shakespeare is that the
historical Shakespeare doesn't seem qualified to have written
literature at such a grand scale. Such authorship more likely rests with an
educated nobleman or
courtier. Although Shakespeare's authorship of his literary
corpus was never doubted in his lifetime, or for centuries thereafter, many other people have been proposed as the real Shakespeare. Prominent in this list are
Christopher Marlowe (1564-1593) and
Sir Francis Bacon (1561-1626).
Mark Twain, as revealed in his 1909 book,
Is Shakespeare Dead?, agreed with the theory that
Bacon was the author of Shakespeare's works. Along the lines of
where have we read this story before, people have searched for
ciphers offering
clues of
Bacon's authorship of Shakespeare's works in the works of both Bacon and Shakespeare.

Sir Francis Bacon (1561-1626).
Bacon was an early proponent of what is now called the scientific method, although his techniques were more empirical than analytical. That's why he's called the father of empiricism, and not the father of the scientific method.
(Via Wikimedia Commons))
U.S. Congressman,
Ignatius L. Donnelly, whom we encountered in connection with the Atlantis myth in a
previous article (Science and the Atlantis Myth, May 18, 2012),
added fuel to the fire with his
book, The Great Cryptogram.[1] In this book, Donnelly presents arguments that Bacon inserted ciphers that expose his authorship into the Shakespeare texts.
The prominent 20th century
cryptographer,
William F. Friedman, examined the question of such
secret codes, and he found that the idea had no merit.[2] Friedman even used the same techniques to "prove" that
U.S. President,
Theodore Roosevelt, was the actual author of Shakespeare's works.
Although the cipher issue is apparently dead, the
computer age has brought us new
tools in the
examination of the authorship of Shakespeare's works. There's no lack of
source material, since there are 36 plays in the
First Folio of 1623. The primary tool is
stylistic analysis, especially
writer invariant text. Such analysis indicates Marlowe's hand in at least some portions of
Henry VI, Part 1 and
Part 2.[3]
There's a converse problem of Shakespeare authorship; namely, which works not in the original folios might actually have been written by him. A prime example is the 1727
play,
Double Falsehood (a.k.a., Double Falshood, or The Distrest Lovers). This is a play written by the
18th century English playwright,
Lewis Theobald (1688-1744), but acknowledged by him as being based on three unnamed Shakespeare
manuscripts. These original manuscripts were lost, probably in a
library fire. All this has engendered another
controversy that this was an original work by Theobald, who tried to generate interest in his play by claiming it to be an
adaptation of a work by Shakespeare.
There is evidence that this play, inspired by the
character, Cardenio, in
Cervantes'
Don Quixote, is actually based on a lost play,
Cardenio, by William Shakespeare and
John Fletcher. Such a play was registered at the
Stationers' Register, September 9, 1653. This presents the question of how much of Double Falsehood, if any, is Shakespeare's own, independent of Theobald and Fletcher.
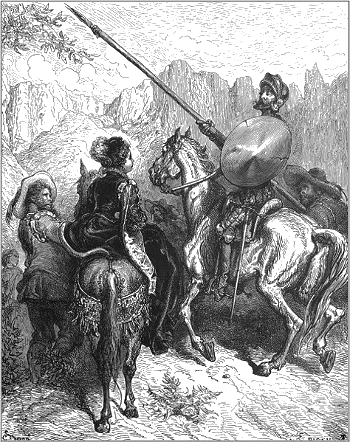
Illustration fifteen from the 1863 edition of Miguel de Cervantes' Don Quixote.
The illustration is by Gustave Doré, who created so many memorable book illustrations, such as those in The Rime of the Ancient Mariner and
Dante's Inferno
(Via Wikimedia Commons.)
Psychologists at the
University of Texas at Austin have done an analysis of Double Falsehood, and they found strong
statistical and
psychological evidence of Shakespeare and Fletcher's co-authorship. To do this, they developed a psychological "signature" for each possible author, and their analysis indicates that the play was not a
forgery by Theobald. Their
research is reported in
Psychological Science.[4-5]
Rather than using the
word counts and
linguistic regularities of
stylistic analysis, the study compares authors' psychological profiles.[5] Says
graduate student,
Ryan Boyd, who co-authored the study with UT-Austin
professor,
James Pennebaker,
"Research in psychology has shown that some of the core features of who a person is at their deepest level can be revealed based on how they use Language. With our new study, we show that you can actually take a lot of this information and put it all together at once to understand an author like Shakespeare rather deeply."[5]
Boyd and Pennebaker analyzed 33 plays by Shakespeare, 12 by Theobald, and 9 by John Fletcher. Extraneous information, such as
publication information, was removed, and
software made possible an analysis of such things as the use of function words (
pronouns,
articles, and
prepositions) and words related to categories such as
emotions,
religion, and
sensory perception. The heavy use of nouns, articles, and prepositions indicates a
formal way of thinking. People who use such words often tend to be emotionally distant, while people who use such words sparingly tend to live in the moment, and they are more
social.[5] In such ways they created a
thematic signature for each author.[5]
By every measure except one, Shakespeare was identified as the most probable author of Double Falsehood.[4-5] Shakespeare's hand is most apparent in the early part of the play, in the first three
acts, while Shakespeare and Fletcher shared authorship of the fourth and fifth acts.[5] Theobald's influence was minor, as confirmed by the assessment that the play's authors were sociable, while Theobald was known to be rigid and abrasive.[5] Says Boyd,
"Honestly, I was surprised to see such a strong signal for Shakespeare showing through in the results... Going into the research without any real background knowledge, I had just kind of assumed that it was going to be a pretty cut and dry case of a fake Shakespeare play, which would have been really interesting in and of itself... We don't need a time machine and a survey form to figure out what type of person Shakespeare was -- we can determine that very accurately just based on how he wrote using methods that are objective and easy to do."[5]
This research was supported by the
National Science Foundation.[5]
References:
- Ignatius Donnelly, "The great cryptogram : Francis Bacon's cipher in the so-called Shakespeare plays," 1887, via the Internet Archive.
- William F. Friedman and Elizabeth S. Friedman, "The Shakespearean Ciphers Examined: An Analysis of Cryptographic Systems Used as Evidence that Some Author Other Than William Shakespeare Wrote the Plays Commonly Attributed to Him," Cambridge University Press, Edition Reissue, April 14, 2011, 334 pp. (via Google Books).
- Hugh Craig and Arthur F. Kinney, Eds., "Shakespeare, Computers, and the Mystery of Authorship," University of Massachusetts, Amherst, August, 2012 (via Amazon).
- Ryan L. Boyd and James W. Pennebaker, " Did Shakespeare Write Double Falsehood? Identifying Individuals by Creating Psychological Signatures With Text Analysis," Psychological Science, vol. 26, no. 5 (May, 2015), pp. 570-582, doi: 10.1177/0956797614566658.
- Shakespeare's plays reveal his psychological signature, Association for Psychological Science Press Release, April 9, 2015.
Permanent Link to this article
Linked Keywords: Riddle; childhood; Grant's tomb; Ulysses S. Grant (1822-1885); President of the United States; wife; Julia Grant (1826-1902); Manhattan; burial; buried; tomb; entombed; William Shakespeare; Shakespeare authorship question; literature; literary; mathematician; Nicolas Bourbaki; pseudonym; 20th century; mathematician; author; anonymity; anonymous; Cobbe portrait; William Shakespeare (1564-1616); oil painting; Droeshout engraving; First Folio; hair; Wikimedia Commons; circumstantial evidence; history; historical; literature; education; educated; nobility; nobleman; courtier; text corpus; Christopher Marlowe (1564-1593); Sir Francis Bacon (1561-1626); Mark Twain; Is Shakespeare Dead?; Baconian theory of Shakespeare authorship; Bible code; cipher; evidence; clue; Baconian cryptology; scientific method; empirical research; analysis; analytical; father; empiricism; Member of Congress; U.S. Congressman; Ignatius L. Donnelly; Atlantis myth; add fuel to the fire; book; cryptography; cryptographer; William F. Friedman; secret code; President of the United States; Theodore Roosevelt; information Age; computer age; tool; Shakespeare attribution studies; source text; source material; stylometry; stylistic analysis; writer invariant text; Henry VI, Part 1; Henry VI, Part 2; play; Double Falsehood; 18th century; English people; playwright; Lewis Theobald (1688-1744); manuscript; library; fire; controversy; literary adaptation; Cardenio; Miguel de Cervantes; Don Quixote; John Fletcher; Stationers' Register; Gustave Doré; The Rime of the Ancient Mariner; Dante's Inferno; psychologist; University of Texas at Austin; statistics; statistical; psychology; psychological; evidence; forgery; research; Psychological Science; word; linguistics; linguistic; style; stylistic; postgraduate education; graduate student; Ryan Boyd; professor; James Pennebaker; language; publication; software; pronoun; article; preposition; emotion; religion; sensory perception; formality; formal; social behavior; thematic; act; time travel; time machine; survey methodology; survey form; National Science Foundation; Ignatius Donnelly, "The great cryptogram : Francis Bacon's cipher in the so-called Shakespeare plays; William F. Friedman and Elizabeth S. Friedman, "The Shakespearean Ciphers Examined: An Analysis of Cryptographic Systems Used as Evidence that Some Author Other Than William Shakespeare Wrote the Plays Commonly Attributed to Him," Cambridge University Press, Edition Reissue, April 14, 2011, 334 pp.; Hugh Craig and Arthur F. Kinney, Eds., "Shakespeare, Computers, and the Mystery of Authorship," University of Massachusetts, Amherst, August, 2012.